Joby Warrick Returns to Bioweapons Security Theater
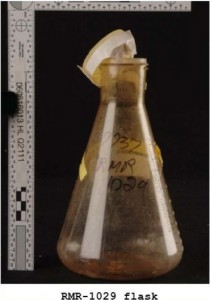
Last night, Joby Warrick put up a dutifully transcribed article in which the intelligence community is warning us to be very afraid that North Korea suddenly has bioweapons capability. Let's hope North Korean anthrax capabilities don't become the next aluminum tubes.

On Pierre Bourdieu Part 1: Vocabulary
A new vocabulary for a new book.

Three Months After Problematic John Sipher Post, Just Security Makes Clear It Let Known Errors Sit for Two Months
Just Security let significant errors go uncorrected for two months in a very prominent post because they didn't like that I had identified the errors in real time.
A Decade Of Trash
Basketball, whether pro or college, does not really start until the first of the year. College football, sand the Army?Navy game - Go Navy! - is done until bowl season really starts, baseball and F1 are off and, so, we are left with the NFL.
And…

"Circumventing" Encryption Is Different than "Weakening" or "Altering" It
While the government told Ron Wyden it has never ordered a company to "alter" encryption using 702 directives, it didn't answer his question about whether it has ordered a company to "circumvent" encryption.
A Bit about Dossiers: You've Been Eating this FUD for Years
Some thoughts about dossiers from a former dossier writer.

Scott Balber's Latest Narrative on Trump Tower
I'm virtually certain the story that some Trump and current Agalarov lawyer Scott Balber has crafted about the June 9 Trump Tower meeting is false.

Two (Three) Possibilities on the "WikiLeaks" Archive Story
There are a few data points that might explain the new "WikiLeaks" archive story.

Cognitive Rot and the Steele Dossier
In which Josh Marshall and Jonathan Chait take the absence of evidence to be evidence.

Christopher Wray Was Doing Great Until He Accused Chad of Spewing Jihadist Propaganda
In his first House Judiciary Committee oversight hearing today, FBI Director Christopher Wray responded to questions about FBI Agent Peter Strzok by explaining there was an ongoing Inspector General investigation into Strzok's role in the…
Ten Years After: A Decade At Emptywheel
It is no secret by now that this blog is celebrating its ten year anniversary. You have seen the posts from Marcy, Jim, Ed and Rayne going throughout the history. This will be my retrospective. But, first, I want to make the ask.
For years,…

Michael Flynn: Serial Doublecrosser
Michael Flynn has a demonstrated history of doublecrossing everyone he deals with.

The Spooks Struggle with Reciprocity
The spooks have done a post on what it means that Shadow Brokers doxed some hackers. I think they're missing a lot.

10 Years of emptywheel: Many Happy Rabbit Holes
Wow, it's been ten years! Time sure flies when you're having fun -- and yes, some of us have a rather perverse sense of amusement, contributors and readers alike. What do you think was the best of this ten years of emptywheel?

Anniversary Top Ten from Ed Walker
My Top Ten posts from emptywheel's first decade

Three Things: Mit Handelsblatther
This morning's buzz was about a subpoena served on Deutsche Bank, which attorney Jay Sekulow denied happened later Tuesday. What really did happen and when? This is an open thread.
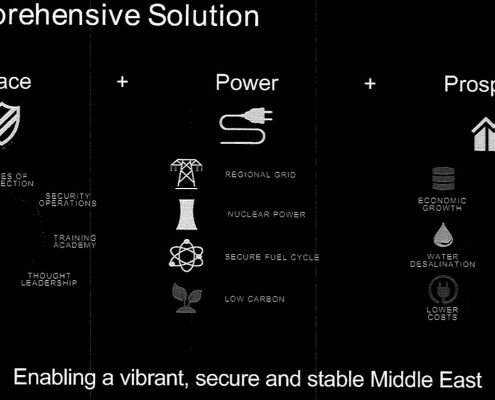
The Ridiculous -- and Chilling -- IP3 Plan for Saudi Economic Diversification
What's really behind the push to diversify the Saudi economy through the construction of nuclear power plants?

Via What Surveillance Intercepts Is the Government Chasing Manafort's Ghost-Writing?
Yeah, I find it funny that Paul Manafort got caught trying to write an op-ed defending his Ukraine work. But I'm just as interested in why Mueller's team effectively told Manafort on what channels they had his surveilled.

A Dragnet of emptywheel's Most Important Posts on Surveillance, 2007 to 2017
A dragnet of emptywheel's most important posts on surveillance.

On the Timing of the Nghia Hoang Pho Plea
The timing of the Nghia Hoang Pho plea may suggest that the government only belatedly came to understand how, by loading a bunch of TAO tools running on his Kaspersky-running computer, made the tools available to a third party hack.
